Standards-based identity security
Use cases
Protect every identity at every stage
Automatically reverify users when risk increases or identity status changes. Their identity wallet already holds their verified credential, so there's no need for full re-enrollment.
Credentials can also be issued to Microsoft Authenticator via Entra Verified ID or the 1Kosmos app.
Workforce
Reverify employee and contractor identity when roles change, access escalates, or suspicious patterns emerge without help desk involvement.
Role changes (promotions, lateral moves, department transfers)
Access level modifications and privileged access escalation
Suspicious activity (unusual login patterns, access from new locations)
Periodic re-verification for privileged access
Contract renewals and employment status changes


Government/Residents
Enable residents to reverify eligibility and identity for benefits and services using their verified credential without document resubmission.
Benefits renewal and recertification
Address or status changes
Suspicious benefit claims
High-value transactions or service requests
Periodic eligibility verification
Customers
Step-up authentication for account changes and high-risk transactions with biometric reverification instead of security questions.
Account modifications (payment methods, contact information)
High-value transactions or equipment rentals
Suspicious activity detection
Account recovery after lockout
Credit limit increases or service upgrades

Customer success
Stopping fraud at scale
Organizations across retail, telecom, and enterprise sectors use 1Kosmos to stop fraud, simplify access, and protect revenue at scale.
$40M+ fraud prevented
Major home improvement retailer across 1,800 stores nationwide
75%+ reduction in targeted fraud
Retail point-of-sale verification for equipment rental and high-value transactions
85K+ weekly verifications
Seamless customer identity verification at scale without operational friction
Millions of daily authentications
Global BPO provider supporting 500K+ workforce across 7K+ applications
3-week deployment
Enterprise-scale rollout with active-active architecture and failover mechanisms
500+ store expansion
Telecom provider scaled from 21-store pilot to nationwide rollout for in-store activations

The break
When identity changes create security gaps
Traditional systems force full re-enrollment for every identity change, creating friction that users bypass. Without a persistent identity wallet, manual reviews fail to scale and miss emerging threats.
Re-enrollment friction drives workarounds
Manual reviews don't scale
Static authentication misses dynamic threats
Legacy MFA can't detect real-time risk
The fix
Instant reverification using existing verified identity
1Kosmos reverifies identity automatically when triggered by lifecycle events or risk signals, using biometrics tied to the user's originally verified credential without re-enrollment.
Architecture
How reverification works
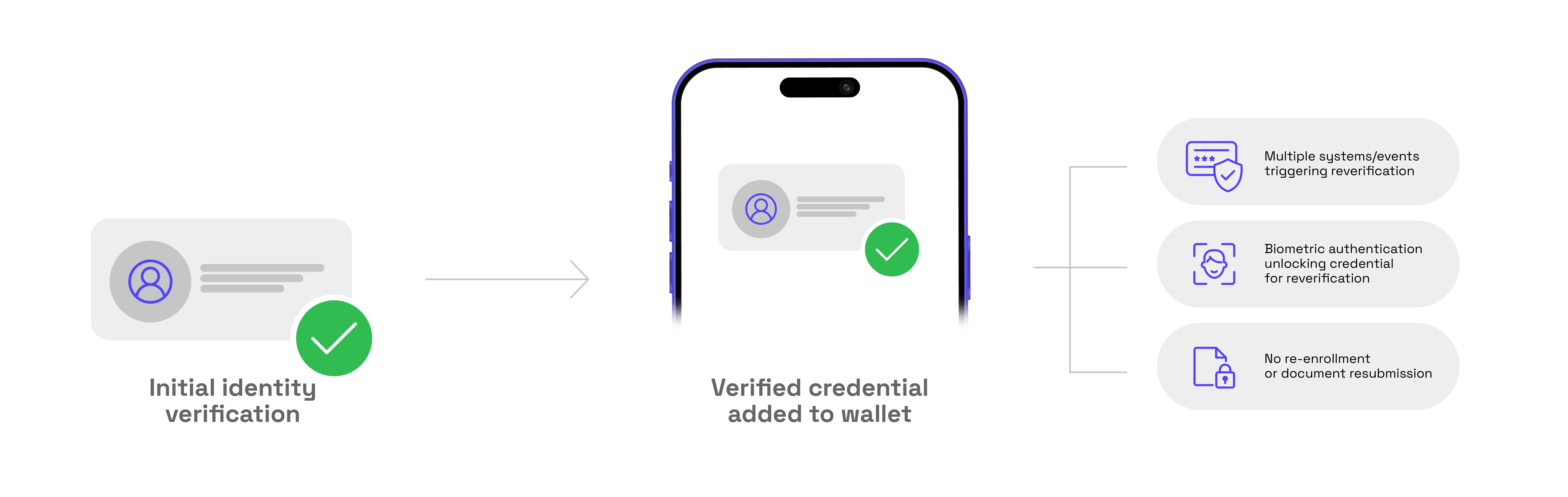
Initial identity proofing creates a portable verified credential stored in a user-controlled digital wallet, enabling reverification across systems without centralized PII storage.
Initial IDV → Verified credential in wallet
Multiple systems/events triggering reverification
Biometric auth unlocking credential for reverification
No re-enrollment or document resubmission
Integrations
Works with Entra & your existing IAM stack
Trigger reverification from IGA platforms, SIEM tools, and IAM systems via API, or deploy continuous authentication across applications with pre-built connectors.
For Microsoft Entra environments, 1Kosmos generates TAP codes for Authenticator onboarding and issues Entra Verified IDs stored directly in the Microsoft wallet.
High-assurance IDV for enterprise & regulated industries
Secure your workforce, partners, patients, and residents with intuitive standards-based identity proofing that’s easy to adopt, even at scale.
?
Financial Services
?
CXM
?
Retail
?
Healthcare
?
Manufacturing
?
Government









