What Does Identity Really Mean in Zero Trust
Why Implement Biometric MFA?
We are all aware of the risks associated with password-based authentication. The proof is in the seemingly endless list of password-based breaches that we see in the news every day. Some companies have attempted to mitigate password risks by adding two-factor authentication (2FA), pesky one-time codes sent via email or text.
The truth is, if you authenticate users who access your systems by way of username-password combinations, even if enhanced by so-called 2FA or MFA methods, then you could improve security a lot, reduce user friction, and cut operating expenses by implementing a biometrics-based solution.
While some solutions claim to solve these problems, many are only exchanging the password for FaceID/TouchID. These legacy apps fail to do the one thing that they are supposed to do – prove who the user is.
Imagine if you could prove each user’s identity every time they logged into a resource. That makes all of the other pillars much easier.
1Kosmos offers identity based Zero Trust- with real biometrics and cryptographic proof of possession and audit.
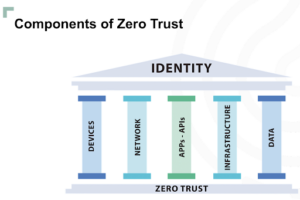
Identity Is One of the 6 Pillars of Zero Trust
Take this diagram:
Other solutions base the “binding” on a username and password exchange which can be done by anyone. This is a problem because when an issue like a lost phone occurs, other solutions fall back to a username, password, 2FA as the bootstrapping process to re-enroll. What do you think the bad guys are going to do with this recovery process? That’s right, exploit it.
How Does 1Kosmos Prove Identity?
When a user downloads the BlockID app and enrolls, they will take a live selfie – This is part of our LiveID. Then, we ask the user for that selfie and compare it to their photo in government issued documents like a passport or a driver’s license. 1Kosmos matches the selfie with the documents, and gives the user a digital certificate that verifies their identity and it binds the account to the proven identity. When users authenticate through LiveID we compare the live selfie with the one taken at enrollment to prove identity and grant access.
To summarize, proving identity and reaching Zero Trust requires one platform that
1) Establishes user-controlled identity
2) Proves authentication with that previously established identity
There are two standards for identity and authentication: NIST 800-63-3 for ID enrollment and strong ID usage, and FIDO2 for passwordless. No platform besides BlockID has combined both of these into one experience. When done right, this single experience can replace many legacy processes and provide a seamless user experience.
In addition to NIST 800-63-3 and FIDO, BlockID’s live biometrics are iBeta certified which validates the reliability of BlockID for accurately performing live biometrics for identity proofing.

There are other key values of the BlockID platform:
– Can be integrated with every system that matters – Remote Access (VPN, Citrix, ZScaler, Appgate, etc.), Desktops (Mac/Windows), SSO systems (Okta/Azure AD/Ping), PAM (Cyberark/Thycotic)
– Can be implemented in parallel, without impacting the existing mechanisms
– Supports multiple company accounts in the same app: Domain Admin, Regular users, AD, Unix Account, etc.
– Supports password reset in the app
– Combines physical and logical access
– Has built in integrity checking
Are you interested in learning more about how the BlockID platform can support your Zero Trust journey? Register for our upcoming webinar, “How to Defeat a Zero Trust Architecture.”
